Anonymity
The ability to do things without giving your name or information such as a photograph that can be mapped to your name. For example, making a purchase with cash without any type of registration.Pseudonymity
The ability to be known under a different name in a particular context. For example, a social network that allows you to register with a user name that differs from your real name.Personality Identifiable Information
Any information that can potentially be mapped back to an individual's identity, particularly their name. For example, a photograph with a clear view of the face can generally be mapped to a name given enough data.Right to Delete
The right to delete, or right to be forgotten, is the right to request that personally identifiable data be deleted. For example, an individual who does something foolish as a teenager who doesn't want this to appear in searches for their name for the rest of their life.Data Liberation
Data liberation is the ability to view, transfer, download and delete all personally identifiable data held by an entity.Right of Access
The legal right to data liberation.Property Rights
The right to own or rent places and devices that are legally yours such that others can't intrude without your permission.Unreasonable Search and Seizure
The right to have your property secure from search and seizure unless authorities have an urgent need based on evidence of a serious crime or a court order.Right Against Self-incrimination
A right to hold back information when it is not in your best interests to share it. For example, the right to remain silent when being questioned by authorities. This may have broad implications for privacy such as a right not to share passwords with authorities.Data Consent
Giving up some level of privacy in order to access products, services, environments, media and communities that have value to you. It is a basic reality of the modern world that personal data is required to deliver most services. For example, you can't travel across borders without presenting a passport.Limited Access
The right to purchase goods and services or participate in the community without giving information. This may limit your level of participation in some reasonable way. For example, a customer may have a right in a particular jurisdiction to make purchases with cash without joining a membership program. This may result in a reasonable limitation such as not receiving membership points.Right to be Let Alone
A right to enjoy your time alone or with friends and family without intrusion. For example, a right to enjoy your home without unsolicited commercial intrusions such as door-to-door salespeople or automated phone calls.Mind Your Own Business
A social norm that prevents people from asking questions in certain areas that are considered private. For example, the norm that it is overly intrusive to ask someone how they vote. These norms differ greatly based on culture.Secrecy
A norm or legal right to keep secrets. For example, a norm that a diary or journal is highly private.Confidentiality
A norm or contract that asks that information shared not be shared with others. For example, the norm that friends will not convey stories of a personal nature that you share.Expectation of Privacy
A reasonable expectation that you will not be observed in a particular situation or place. For example, the expectation that you will not be observed or recorded in a hotel room.Data Aggregation
The process of building big databases from small ones. For example, a social network that purchases data about you from loyalty card programs to know everything that you have purchased at a store. This could then be tied to large profiles that may be shared with others who then aggregate the personally identifiable information further.Data Breach
Data, potentially including personally identifiable information, that leaks to unknown entities due to a failure of information security.Panopticon
A prison design that allows for constant surveillance. This is often used as an analogy for modern surveillance of public space or perhaps even private spaces such as the home.Transparency
Personally identifiable information that is collected and used in an open way with candid communication that explains how it is used. This can be contrasted with secretive collection and use of data without the knowledge of identifiable individuals.Privacy by Design
A term for privacy as a design goal for information technology. This generally involves minimizing the amount of data collected and putting up virtual walls so that data can't be aggregated. Privacy by design can be implemented to provide rich services while guaranteeing anonymity or at least a reasonable level of privacy.Data Anonymization
Transforming data to make it difficult or impossible to identify individuals. This allows data to be used for important purposes such as medical research without compromising the privacy of individuals.Overview
Privacy is the right to live aspects of your life unobserved. This has always existed but is far more complex in a world of computing technologies that allow for the collection, transfer and processing of copious amounts of information.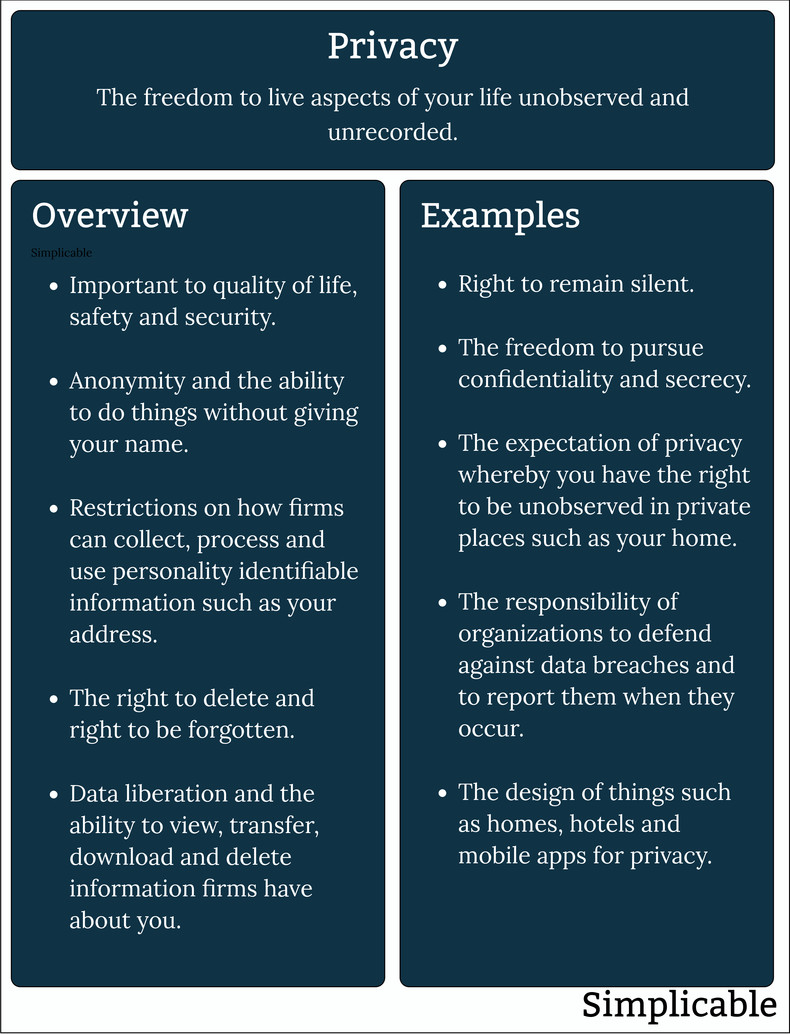
Notes
The article above is at the concept level. For example, rights stated above may not be legally protected in your jurisdiction.| Summary: Privacy Examples | ||
Type | ||
Definition | The freedom to live aspects of your life unobserved and unrecorded. | |
Related Concepts | ||