Purpose
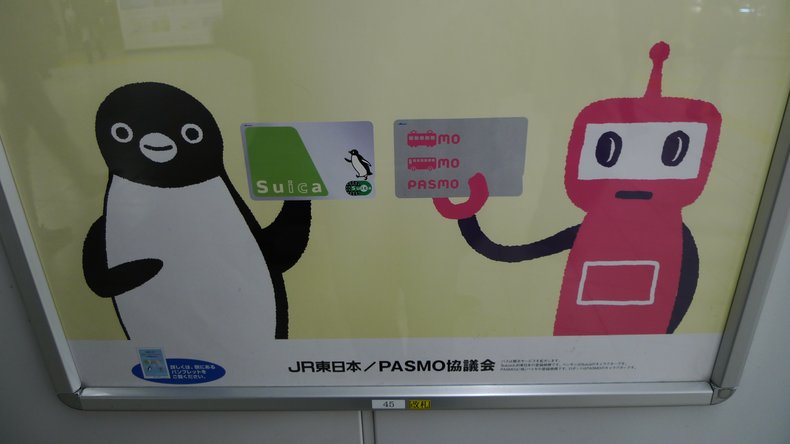
Smart cards are commonly used for payments, public transport, security ids, government identification such as health cards and to enhance computer and ecommerce security. In many cases, a single card can be used for multiple purposes such as a transit card that can store electronic cash for payments. Smart cards may be contactless whereby they can communicate with devices in close proximity. Alternatively, they may require contact such as being inserted into a slot.| Overview: Smart Card | ||
Type | ||
Definition | A wallet-sized card with embedded integrated circuits. | |
Value | Typically used to offer secure and convenient services such as payments or access to services such as transit and healthcare. | |
Related Concepts | ||