Distributed Denial of Service Attacks
A distributed denial of service attack is the use of many computers to flood a service such as a website with enough requests to render it unavailable. Such attacks send requests at high speed without bothering to wait for a response. Network protocols could theoretically support proof-of-work requests that could be used to slow attacks.High Frequency Traders
If a stock exchange wanted to slow down high frequency trading algorithms they could force them to complete proof-of-work tasks. Human traders might be able to bypass such requirements with user authentication techniques. This could theoretically reduce algorithms to human speed in executing trades, if that was the goal of a particular exchange.Cryptocurrency
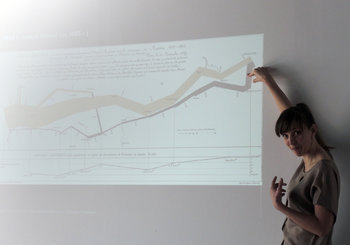
Cryptocurrencies may use proof-of-work to mine new currency. In order for the currency to be valuable, this needs to be hard to do. Math problems for mining currency may require quintillions of processing loops to mine a single unit of currency. This consumes a great deal of electricity and other resources such as CPUs and land. If all the world's currency was mined like this it may have a significant environmental impact.| Overview: Proof Of Work | ||
Type | ||
Definition (1) | Requiring a solution to a mathematical problem in order to complete a valid request or transaction. | |
Definition (2) | An information security technique that requires requests to show evidence of having completed a task of predictable complexity. | |
Definition (3) | Slowing technology down by requiring mathematical problems to be solved. | |
Related Concepts | ||