
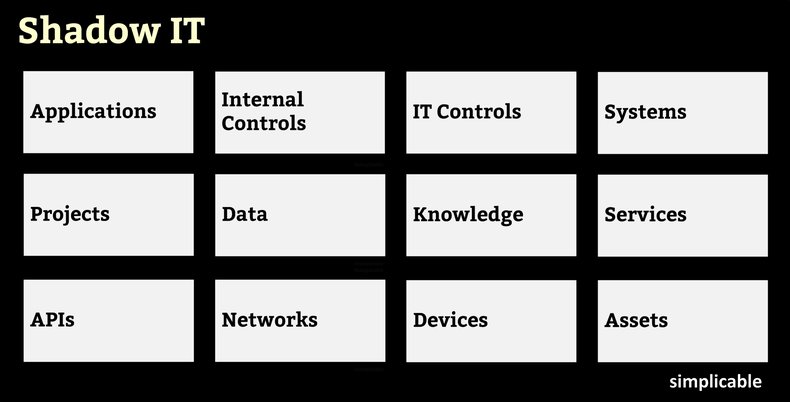
Applications
Installation of applications or apps. This can represent an information security risk as an application may contain vulnerabilities or malicious code that users are unlikely to notice.Internal Controls
In some cases, employees install tools to bypass internal controls. For example, traders at a bank could install an encrypted messaging app to bypass compliance constructs such as a Chinese wall.IT Controls
Disabling IT controls that are perceived as inefficient or obstructive. For example, disabling a virus scanner on a system.Systems
Installation, development and configuration of systems that perform a business function such as automation or data integration. Typically results in a fragmented architecture that is highly inefficient. There is also potential for operational problems such as outages caused by undocumented systems.Projects
Software or infrastructure projects that fly under the radar without going through official channels such as the CIO and IT governance. This can occur due to office politics whereby an executive with significant authority is uncooperative with IT.Data
Developing data repositories such as a spreadsheet used to manage customer or product data. Such data may be prone to data loss.Knowledge
Knowledge repositories that are hidden from the rest of the organization such as a folder filled with team documents that aren't checked into a document management system. Leads to knowledge loss and knowledge waste.Services
Use of external services such as a cloud-based sales tool. Can result in a variety of commercial, security and productivity issues.APIs
Software developers who download and use APIs without proper verification of legal or security issues regarding its use.Networks
An employee who does work using the public internet when a more secure network such as a VPN is required according to policy.Devices
Employees who store company data on personal devices or connect outside devices to the private networks of an organization.Assets
Acquiring tangible or intangible assets that aren't managed by processes such as procurement, asset management, financial management, license management, service management and compliance. For example, an employee registers a domain name using her name and credit card for a firm. Customers start using the site and it remains under her control when she leaves the company.| Overview: Shadow IT | ||
Type | ||
Definition | The unauthorized use of technology within an organization. | |
Related Concepts | ||































